New Delhi, March 31 -- Modern digital platforms no longer operate as bounded systems. They function as ecosystems-dense networks of third-party integrations, developer extensions, AI services, data processors, and infrastructure dependencies that collectively shape user outcomes at global scale.
In these environments, trust is not a policy objective or a contractual assumption. It is a runtime property of the system itself, and it must be engineered accordingly.
Yet most organizations continue to govern these ecosystems using static, document-driven models: onboarding questionnaires, annual reviews, contractual attestations, and post-incident audits. These approaches were designed for linear vendor relationships-not for continuously evolving digital ecosystems.
The result is a widening gap between governance intent and production reality.
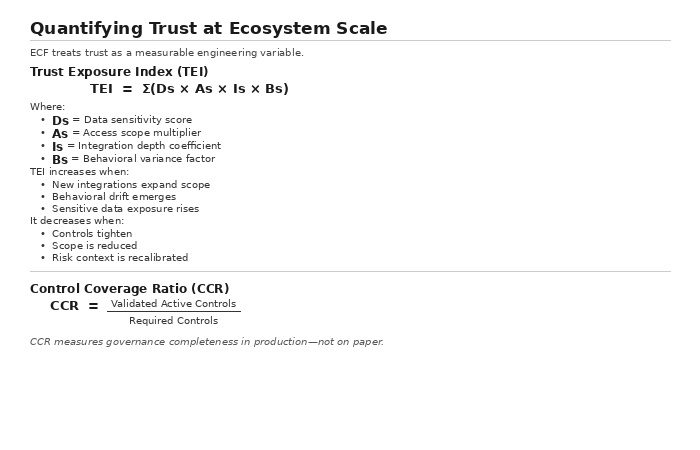
This article introduces a product-level architectural model-the Ecosystem Control Fabric (ECF)-that reframes trust as a measurable, enforceable, continuously evaluated system attribute. Rather than treating governance as external oversight, ECF embeds safeguards directly into the technical fabric of the platform.
Why Traditional Governance Models Fail at Ecosystem Scale
Conventional third-party risk management (TPRM) and compliance programs are structurally misaligned with modern systems:
They rely on point-in-time assessments. They assume stable integration boundaries. They separate legal accountability from technical enforcement. They treat certification as static rather than behavioral.
In practice, ecosystem risk is dynamic:
Vendors evolve services post-onboarding. AI models retrain and shift behavior. Data access patterns drift silently. Infrastructure dependencies introduce transitive exposure.
Zero Trust architectures improve identity-based enforcement but stop short of ecosystem accountability. They answer who can access a system-not whether that access remains appropriate under evolving context, behavior, and impact.
The failure pattern is consistent: risk accumulates invisibly across integrations until a single event exposes systemic weakness.
This is the gap the Ecosystem Control Fabric is designed to close.
The Ecosystem Control Fabric (ECF)
The Ecosystem Control Fabric is a layered governance architecture that embeds trust enforcement into runtime system behavior.
Instead of governance wrapping around the product, governance becomes part of the product.
ECF Core Layers
1. Governance Abstraction Layer Legal, regulatory, and contractual obligations are translated into machine-readable control primitives. Policies are no longer PDF documents-they are structured constraints that can be evaluated programmatically.
2. Risk Context Layer Each integration is assigned contextual risk attributes:
Data sensitivity tier Access scope breadth Integration depth Population exposure Geographic regulatory exposure Decision criticality
Risk is contextual, not binary.
3. Control Specification Layer Risk context drives enforceable technical controls:
Purpose-bound access tokens Rate and volume throttling Isolation requirements Data minimization enforcement Behavioral thresholds
These controls are declarative and versioned.
4. Runtime Enforcement Layer Controls are enforced at:
API gateways Service mesh sidecars Data pipelines Event streaming boundaries AI inference endpoints
Trust decisions are executed per transaction.
5. Telemetry & Audit Layer Every trust decision generates:
Signed audit artifacts Behavioral signals Control state snapshots
This enables deterministic reconstruction of governance posture at any point in time.
Ecosystem Risk Score (ERS) ERS aggregates:
TEI values CCR gaps Anomaly detection signals Certification staleness
ERS becomes a routing input into runtime enforcement logic. Governance influences traffic decisions-not just reports.
Visual Model: Concentric Trust Zones with Embedded Enforcement Nodes
Layer 1: Core Platform Zone (Highest Trust Tier)
Internal microservices Data stores Model training pipelines Administrative systems Full governance coverage Lowest TEI baseline
Controls:
Strict identity and workload authentication Service-to-service policy enforcement Full telemetry capture
Layer 2: First-Party API Boundary
Public APIs Internal developer interfaces SDK access points
Enforcement Nodes:
API gateway with policy engine Purpose-scoped access tokens Rate control modules Telemetry emitters
All traffic crossing this boundary passes through enforcement logic.
Layer 3: Verified Partner Integration Zone
Contracted vendors Strategic integration partners High-volume data processors
Controls:
Control inheritance contracts Runtime attestation verification Behavioral scoring inputs Isolation policies (logical tenancy boundaries)
Each integration receives a dynamic ERS that influences privilege scope.
Layer 4: Open Ecosystem / Marketplace Tier
Plugin developers External AI services Low-trust extensibility modules
Controls:
Strict least-privilege tokens Behavioral anomaly detection Elevated monitoring frequency Automatic privilege downgrades upon drift
TEI weighting is higher in this tier due to unpredictable variance.
Layer 5: External Consumers / Edge
Data recipients Downstream processors Federated services
Controls:
Data watermarking Lineage tagging Outbound flow validation Purpose binding checks
Telemetry Loop (Cross-Cutting Plane)
Across all zones:
Enforcement nodes emit telemetry to a centralized risk engine. Risk engine recalculates TEI and ERS. Policy engine updates enforcement parameters. Updated constraints propagate back into runtime.
This creates a closed-loop governance system. Trust becomes adaptive.
Why ECF Is Structurally Different
Capability Traditional TPRM Zero Trust Ecosystem Control Fabric Assessment Timing Periodic Continuous Continuous Enforcement Layer Outside System Identity Layer Runtime Service Layer Trust Model Static certification Identity-based Contextual + Behavioral Governance Evidence Documentation Logs Deterministic telemetry artifacts Ecosystem scalability Limite Moderate Native
ECF is not incremental. It repositions governance as a distributed systems discipline.
National and Sector-Level Implications
This architecture has implications beyond any single company. Sectors operating high-risk digital ecosystems include:
Financial services API banking platforms Healthcare interoperability networks AI model marketplaces Large consumer platforms with third-party extensibility Critical infrastructure SaaS providers
In these environments, failure is rarely a single breach. It is a gradual erosion of trust posture across integrations. ECF makes that erosion detectable and correctable in real time.
The Governance Evolution Thesis The legacy model treated compliance as a wrapper around product development. Controls were added after systems were built.
That model is collapsing under ecosystem complexity. The next decade of digital platform governance will be defined not by stronger audits but by embedded control fabrics.
Organizations that engineer trust into runtime architecture will not merely reduce regulatory exposure. They will gain competitive advantage in markets where trust is measurable, programmable, and demanded.
Trust at scale is not a compliance outcome. It is a systems design achievement. And the platforms that lead in this domain will define the operational standard the rest of the industry must meet.
NOTE : No TechCircle Journalist was involved in the creation/production of this content.
Published by HT Digital Content Services with permission from TechCircle.
